When you create a new Azure subscription in your Azure Active Directory (Azure AD) tenant, by default it will be automatically added under the Root management group. This new subscription will then inherit all the governance conditions, like Azure Policy assignments and Azure role-based access control (RBAC) permissions applied to this management group.
But in many cases customers require a less or in some cases a more restrictive set of control for their new subscriptions.
Luckily, nowadays you have the option to configure another dedicated management group as the default management group for new subscriptions. In this way customers can apply policies and/or Azure role assignments which are more suited for their new subscription(s) to this separate management group.
This will not only make it easier for their Azure Administrators to start their greenfield or brownfield deployments and even cloud migrations. But it will also allow users who may or can make use of an Azure MSDN or Visual Studio subscription to start experimenting with resources that are not (yet) allowed in the development, production and even test environment.
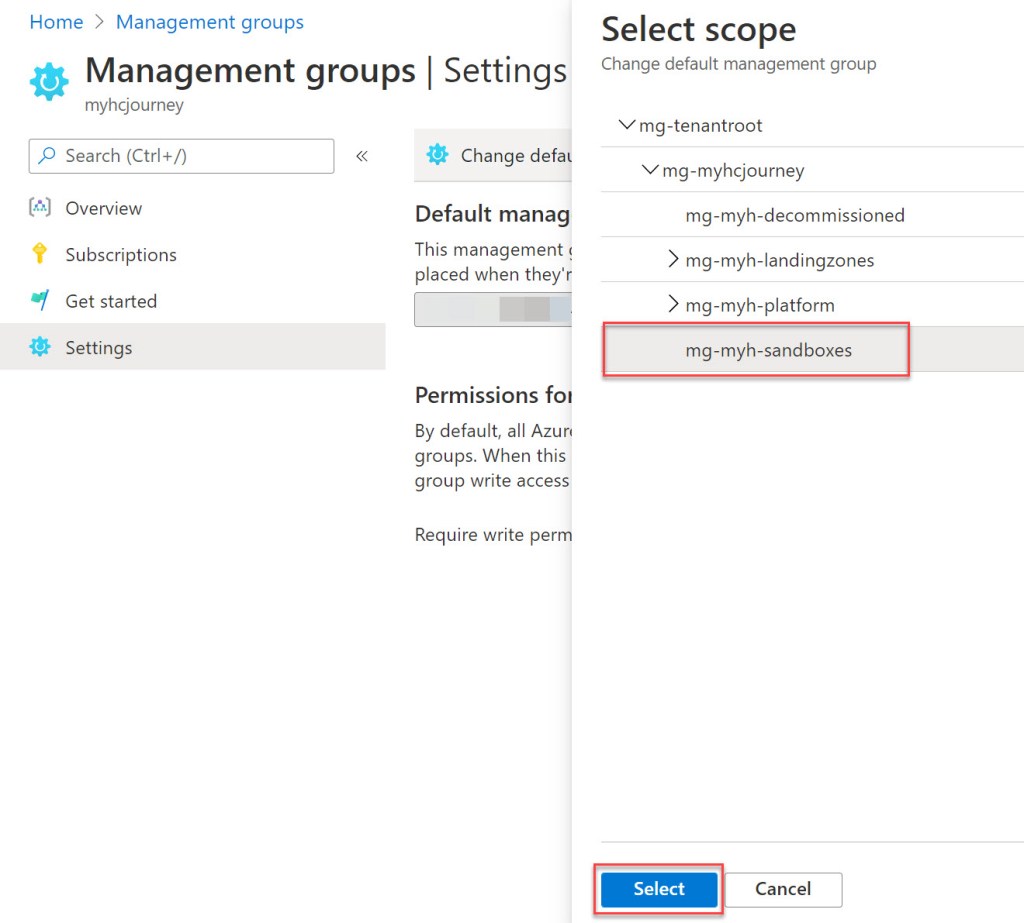
This makes a top-level sandbox management group a good candidate as the new default management group.
If you want to read some more about how Azure management groups can help you organize your resources and subscriptions, you can do so via the following Microsoft Docs link: Azure management groups documentation
Change the default management group for new subscriptions
Logon to the Azure Portal with a user who has the Global Administrator role.
To be able to change the default management group this user requires the User Access Administrator (elevated access), the Owner and the Hierarchy Settings Administrator role.
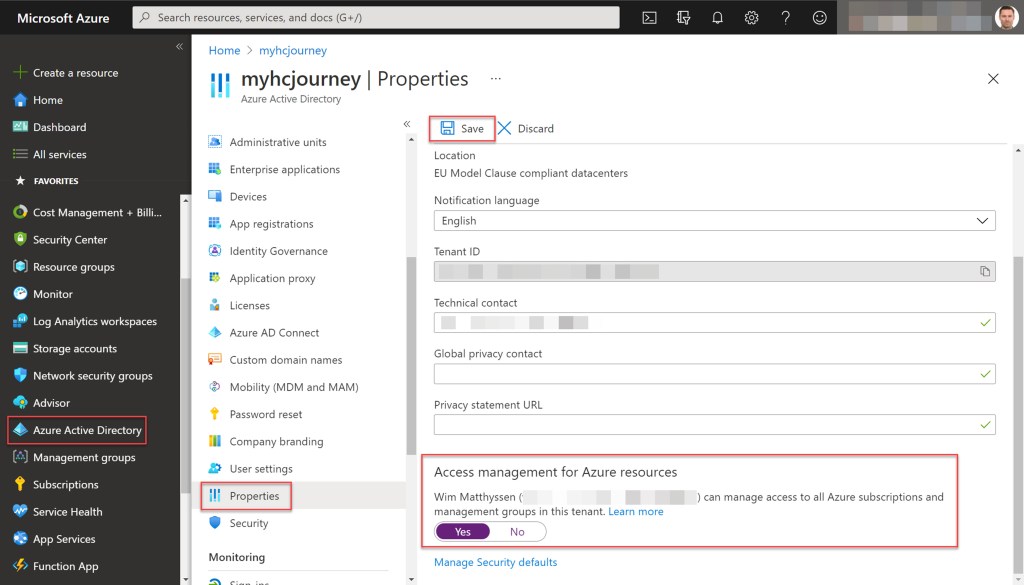
To elevate the access of the signed in Global Administrator, open Azure Active Directory, select Properties. On the Properties window under Access management for Azure resources, set the toggle switch to Yes. Click Save to apply the change.
To set the Owner and Hierarchy Settings Administrator role on the Tenant Root group scope you need to use Azure PowerShell or CLI. Open Azure Cloud Shell or Windows Terminal and run the following Azure PowerShell cmdlets (change “your global admin account” with your own account) to set both RBAC roles.
## Assign the Owner role on your Tenant Root Group
New-AzRoleAssignment -SignInName "your global admin account" -RoleDefinitionName "Owner" -Scope "/"
## Assign the Hierarchy Settings Administrator role on your Tenant Root Group
New-AzRoleAssignment -SignInName "your global admin account" -RoleDefinitionName "Hierarchy Settings Administrator" -Scope "/"


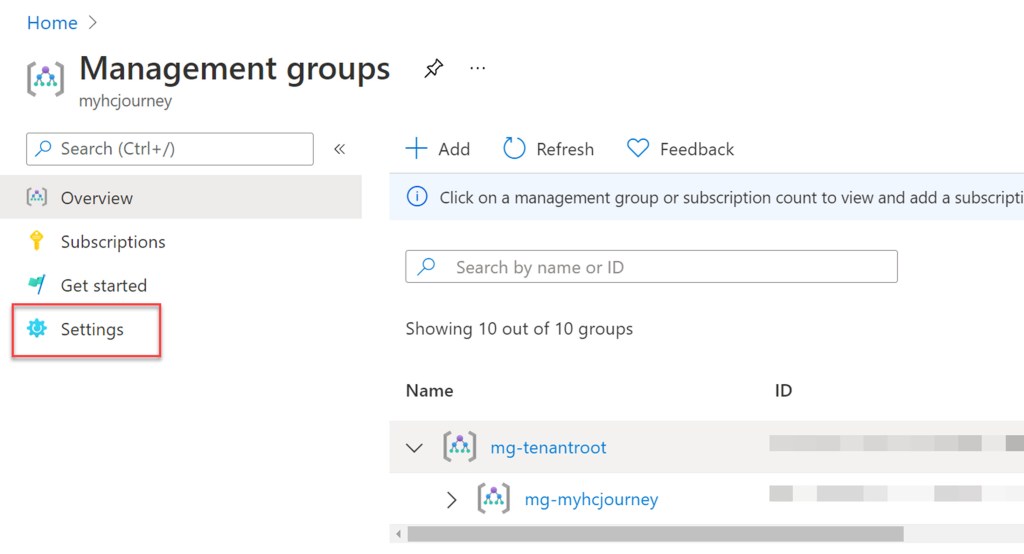
When the proper Azure role assignments are set, go to the global search box and type management. Then select Management groups.

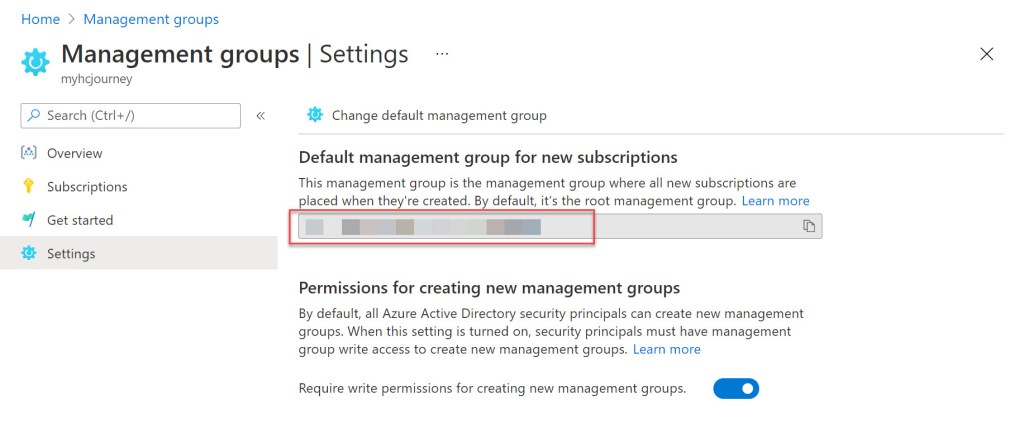
When the Management groups window opens, select Settings.
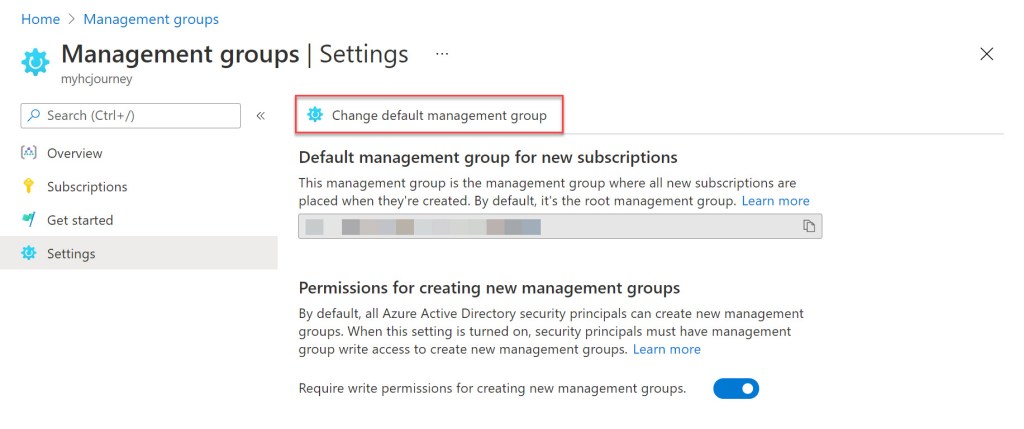
Under Settings, click on the Change default management group button.
If the Change default management group button is disabled, you should check if the account your using has all the proper RBAC rights set.
On the Select scope window, select the management group you want to set as the default one. Click Select to apply the new setting.
You can validate the change by checking the Management group ID under the Default management group for new subscriptions section.
Conclusion
All new Azure subscriptions are placed under the root management group by default.
But as a best practice it is better to configure a default dedicated management group for new subscriptions with less restrictive settings.
That is why a top-level sandbox management group is a good candidate as the default management group for new subscriptions.

Amazing blog post! I’m working for a Spanish Company where we are currently adopting the Cloud Adoption Framework, is there still a need for a default subscription definition then?
LikeLike
Hi David, determining a default management group for all new subscriptions is also an element included in Microsoft’s CAF. It’s something I now describe and implement by default in any design or implementation for any new customers Azure environment. In my opinion it will help you defining a better hierarchy and give you more control on any newly added subscription. But like most times it all depends on the size of the environment and on the way you want to implement your governance structure.
LikeLike
Great article Wim! I’ve just added this to my standard practice list! 😊
Thanks for this.
LikeLiked by 1 person
Pingback: Azure PowerShell script: Build a management group tree hierarchy – Wim Matthyssen